Choosing an outsourcing partner is not just a delivery decision. It is a business risk decision. The right vendor can help you scale faster, access specialist skills, and reduce delivery pressure. The wrong vendor can create security gaps, hidden costs, missed deadlines, weak documentation, and long-term dependency. That is why outsourcing due diligence matters. Before signing a contract, you need a clear way to assess whether the vendor is secure, financially stable, technically capable, and operationally reliable.
This article gives you a practical IT outsourcing due diligence checklist to evaluate vendors before you make a long-term outsourcing decision.
What’s included in an IT Outsourcing Due Diligence Checklist?
Use this IT outsourcing due diligence checklist to assess whether a software outsourcing vendor can deliver securely, reliably, and transparently. The checklist should cover security, compliance, delivery capability, financial stability, operational resilience, contracts, intellectual property, and exit planning.
Security & Compliance
- Does the vendor hold ISO 27001, SOC 2, or another relevant security certification?
- Is a Data Processing Agreement or similar legal agreement in place?
- How does the vendor handle GDPR, data residency, and client data protection?
- What access control, password, and multi-factor authentication policies are used?
- Does the vendor have a documented incident response process?
- Can the vendor provide recent penetration test, vulnerability scan, or security audit evidence?
Delivery Capability
- Has the vendor delivered similar software projects before?
- Can they provide relevant case studies or client references?
- What development methodology, QA process, and reporting cadence do they use?
- How do they manage scope changes, delays, and technical risks?
- Who owns code quality, architecture decisions, and documentation?
Financial & Company Background
- Is the company legally registered?
- Who are the board members, directors, or leadership team?
- Can the vendor show signs of financial stability?
- Are there any tax, legal, financial, or reputational red flags?
Operational Resilience
- Does the vendor have a business continuity plan?
- What happens if key developers leave the project?
- How does the vendor handle onboarding and knowledge transfer?
- What communication rhythm and reporting tools are used?
- How does the vendor maintain visibility across tasks, risks, and progress?
Contract, IP & Exit Terms
- Who owns the source code and final deliverables?
- Are intellectual property rights clearly defined?
- What service-level agreements or response times are included?
- What happens if the partnership ends?
- Is there a clear exit, handover, or knowledge transfer plan?
If your vendor cannot answer these questions clearly, you should slow down the decision. A strong outsourcing partner should be able to show how they work, how they manage risks, and how they protect your business before the contract is signed.
What is outsourcing due diligence?
Outsourcing due diligence is the structured process of evaluating a potential outsourcing vendor before entering a business relationship. It helps you verify whether the vendor is technically capable, financially stable, legally compliant, secure, and operationally reliable.
In software development, due diligence is especially important because the vendor may handle source code, business logic, customer data, internal systems, infrastructure access, and long-term product knowledge. That means you are not only buying development capacity. You are giving an external partner access to critical parts of your business.
A good due diligence process helps you answer one practical question: Can this vendor deliver what we need without creating unacceptable business, security, or operational risk?
Why is due diligence important before outsourcing software development?
Outsourcing can help your company move faster, but it also increases dependency on an external team. Without proper due diligence, you may discover important risks only after the project has started.
By then, it is harder to change direction. You may already have shared access, committed budget, transferred knowledge, or built part of your product around the vendor’s team.
Due diligence helps you reduce four major risks.
Security and compliance risk
Software vendors often need access to repositories, staging environments, production systems, documentation, user data, or business-sensitive information. If the vendor has weak security practices, your company may be exposed to data breaches, unauthorized access, or compliance gaps.
For European companies, this is especially important when personal data is involved. GDPR Article 28 requires processing by a processor to be governed by a contract or legal act that defines the subject matter, duration, nature, purpose, data types, categories of data subjects, and obligations of both parties.
Delivery failure risk
A vendor may look strong in a sales meeting but still fail during execution. Common problems include unclear team structure, weak project management, poor QA, limited documentation, and slow escalation when issues appear.
Due diligence helps you check whether the vendor has proven delivery processes before you depend on them.
Hidden cost and scope risk
Low pricing can hide unclear assumptions. If the vendor has not clarified scope, communication rhythm, quality standards, or change request processes, the project can become more expensive than expected.
A proper review helps you understand what is included, what is excluded, and what happens when requirements change.
Vendor lock-in risk
If source code ownership, documentation, knowledge transfer, and exit terms are unclear, your company can become dependent on one vendor. This makes it difficult to switch partners, bring development in-house, or continue the project with another team.
Good due diligence protects your future flexibility.
What documents should you request from an outsourcing vendor?
A reliable outsourcing vendor should be able to provide evidence, not only promises. Before you sign, ask for documents that help you verify company background, security practices, compliance readiness, delivery capability, and contract clarity.
| Area | Documents to request |
|---|---|
| Company background | Business registration, company structure, leadership profile, office location, ownership information |
| Security | Security policy, access control policy, ISO 27001 or SOC 2 evidence, incident response process, penetration test or vulnerability scan reports |
| Compliance | Data Processing Agreement, GDPR process, privacy policy, sub-processor list, data handling procedure |
| Delivery | Case studies, project plan sample, QA process, communication plan, reporting template, team CVs |
| Finance | Annual report, tax documents, insurance, financial stability indicators |
| Legal | Master Service Agreement, Statement of Work, SLA, IP ownership terms, termination clauses |
| Operations | Business continuity plan, disaster recovery process, employee retention information, onboarding and handover process |
For contracts involving personal data, the UK ICO explains that processor contracts should include minimum terms such as processing only on documented instructions, confidentiality, security measures, sub-processor rules, data subject rights support, end-of-contract provisions, and audit rights.
How do you evaluate an outsourcing vendor step by step?
A checklist is useful, but it works best when used inside a structured review process. Here is a practical step-by-step approach.
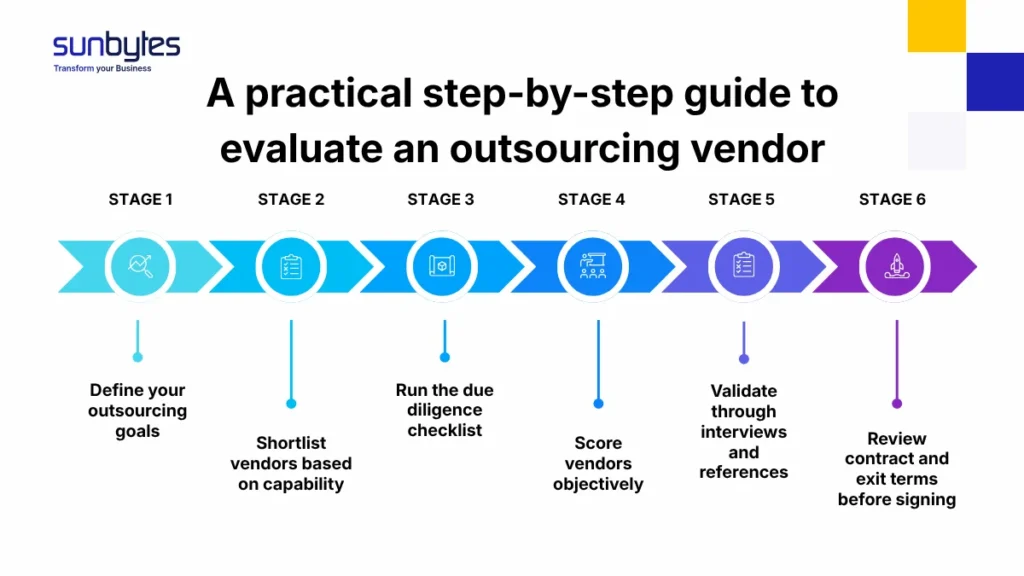
Step 1 — Define your outsourcing goals
Before evaluating vendors, clarify why you are outsourcing.
Are you trying to reduce delivery pressure? Add niche technical skills? Build a product faster? Modernize an existing system? Improve QA? Support long-term maintenance?
Your goal affects the type of vendor you need. A company looking for short-term development support should not evaluate vendors in the same way as a company looking for a long-term dedicated software team.
Define:
- Project scope
- Required technical skills
- Expected timeline
- Budget range
- Security and compliance requirements
- Preferred engagement model
- Internal stakeholders involved
- Success metrics
This gives you a baseline for comparing vendors consistently.
Step 2 — Shortlist vendors based on capability
Once the goal is clear, shortlist vendors that match your project type and business context.
Look at:
- Relevant industry experience
- Technology stack
- Similar case studies
- Team size and seniority
- Communication style
- Time zone fit
- Security and compliance maturity
- Delivery model
- Client references
Avoid shortlisting vendors only because they are affordable. Price matters, but a low-cost vendor without the right experience can create more management work for your internal team.
Step 3 — Run the due diligence checklist
Use the IT outsourcing due diligence checklist to review each vendor across the same categories:
- Security and compliance
- Technical delivery capability
- Financial and company background
- Operational resilience
- Communication and reporting
- Contract and IP terms
- Exit and handover process
Do not treat this as a box-ticking exercise. The goal is not just to collect documents. The goal is to understand how the vendor actually works and whether their process matches your risk level.
Step 4 — Score vendors objectively
After collecting answers, score each vendor using a simple risk matrix.
| Criteria | Weight | Vendor A | Vendor B | Vendor C |
|---|---|---|---|---|
| Security & compliance | 25% | |||
| Technical capability | 25% | |||
| Delivery process | 20% | |||
| Financial stability | 10% | |||
| Communication fit | 10% | |||
| Contract & IP clarity | 10% |
This helps you avoid choosing based on the best sales presentation. A scoring matrix makes trade-offs clearer. For example, one vendor may be cheaper but weak on security. Another may cost more but provide stronger delivery governance, better documentation, and clearer ownership terms. The better choice depends on your business risk tolerance.
Step 5 — Validate through interviews and references
Documents are useful, but interviews reveal how the vendor thinks. Speak with the people who will be involved in delivery, not only the sales team. Ask to meet the delivery manager, technical lead, QA lead, or security contact if relevant.
Useful questions include:
- How do you handle unclear requirements?
- How do you report risks?
- What happens when a milestone is delayed?
- How do you manage code reviews?
- How do you onboard new developers?
- How do you handle knowledge transfer?
- How do you escalate critical issues?
You should also ask for client references or case studies that match your project type. A vendor with relevant experience should be able to explain what problem they solved, how they worked, and what results were achieved.
Step 6 — Review contract and exit terms before signing
The final step is legal and operational review.
Before signing, make sure the contract clearly defines:
- Scope of work
- Deliverables
- Timeline
- Pricing model
- Payment terms
- Communication responsibilities
- Service levels
- Security requirements
- Data protection obligations
- IP ownership
- Source code ownership
- Confidentiality
- Termination rights
- Exit process
- Handover expectations
The exit terms are often ignored, but they are critical. A responsible vendor should support continuity if the partnership ends. That includes documentation, repository access, credentials handover, technical walkthroughs, and knowledge transfer.
What are the biggest red flags in outsourcing due diligence?
A vendor does not need to be perfect, but they should be transparent. If they cannot explain their process, provide evidence, or answer basic risk questions, that is a warning sign.
Here are the most common outsourcing red flags to watch for.
No clear security documentation
If the vendor cannot explain access control, data handling, secure development practices, or incident response, they may not be ready to handle sensitive systems.
Security should not be improvised after the project starts.
Vague GDPR or data protection answers
If your project involves personal data, the vendor must understand how data is processed, stored, accessed, transferred, and deleted. Vague answers like “we are GDPR-friendly” are not enough.
Ask for the actual process, contract terms, and responsibilities.
No relevant case studies
A vendor may have general development experience but not the right experience for your project. If they cannot show similar work, you may need to spend more time validating their capability.
Unclear team structure
You should know who will work on your project, what roles they play, how much time they are allocated, and who is responsible for delivery quality.
If the vendor cannot explain the team setup, expect communication issues later.
Very low pricing with unclear scope
A price that looks too good can become expensive if it excludes QA, documentation, project management, security reviews, or support.
Always ask what is included and what will be charged separately.
Weak communication during the sales process
The sales process is often the vendor’s best behavior. If communication is already slow, unclear, or inconsistent before signing, it may become worse during delivery.
No business continuity plan
People leave. Systems fail. Incidents happen. A vendor should have a plan for continuity, backup, disaster recovery, and knowledge transfer.
No exit or handover plan
If the vendor cannot explain what happens when the partnership ends, your company may face vendor lock-in.
A good outsourcing relationship should protect both delivery and independence.
How should you compare outsourcing vendors after due diligence?
After the due diligence process, do not compare vendors only by hourly rate. Compare the total value and risk profile. A stronger vendor may cost more per hour but reduce hidden costs by improving delivery speed, quality, communication, and documentation. A cheaper vendor may require more internal supervision, more rework, and more time from your team.
Use these questions to make the final decision:
- Which vendor understands our business goal best?
- Which vendor has the strongest evidence of similar delivery?
- Which vendor gives us the most confidence on security and compliance?
- Which vendor communicates clearly and consistently?
- Which vendor gives us the best team structure?
- Which vendor has the clearest contract, IP, and exit terms?
- Which vendor reduces pressure on our internal team instead of increasing it?
For technology and software supply chains, NIST describes cyber supply chain risk management as identifying, assessing, and mitigating risks across interconnected ICT and operational technology supply chains throughout the system life cycle, including design, development, deployment, maintenance, and disposal. That same mindset applies to outsourcing. You are not only selecting a vendor for today’s sprint. You are selecting a partner that may affect your product, systems, data, and delivery capacity for years.
How does Sunbytes support outsourcing due diligence?
Sunbytes is a Dutch-led technology company with headquarters in the Netherlands and a delivery hub in Ho Chi Minh City, Vietnam. For companies evaluating software outsourcing partners, we help make due diligence easier by giving clarity on team structure, delivery process, communication rhythm, security practices, and long-term collaboration models.
Instead of asking clients to trust a sales promise, we help them review the practical details that matter before cooperation starts: who will work on the project, how delivery is managed, how quality is controlled, how communication is handled, and how risks are reduced throughout the engagement.
Digital Transformation Solutions
- Digital Transformation Solutions: Sunbytes helps companies build, modernize, and maintain digital products with experienced engineering teams. This includes custom software development, QA/testing, maintenance, support, and modernization work. For outsourcing due diligence, this means you can assess not only the team’s technical skills but also how delivery is structured, how quality is managed, and how the project can scale over time.
- CyberSecurity Solutions: Security should be part of delivery from the beginning, not added at the end. Sunbytes supports clients with a secure-by-design mindset, security testing, risk reduction, and compliance readiness. This helps companies evaluate whether their outsourcing partner can protect code, systems, access, and sensitive data during the engagement.
- Accelerate Workforce Solutions: Some companies do not only need a vendor. They need extra capacity, long-term technical talent, or a dedicated team that works as an extension of their own organization. Sunbytes supports this through dedicated developers, dedicated teams, Team as a Service, and workforce support. This helps companies scale delivery while keeping collaboration, communication, and management structure clear.
If you are reviewing outsourcing partners and want a secure, transparent, and reliable delivery setup, contact Sunbytes to discuss your project requirements and due diligence process.
FAQs
An outsourcing due diligence checklist is a structured list of questions and documents used to evaluate a vendor before signing a contract. It helps companies review security, compliance, technical capability, financial stability, operational processes, contract terms, and potential risks.
IT outsourcing due diligence should include vendor background, security practices, data protection processes, compliance readiness, technical capability, delivery methodology, team structure, financial stability, legal terms, intellectual property ownership, and exit planning.
The timeline depends on project complexity and risk level. A simple vendor review may take a few days. A complex software outsourcing decision involving sensitive data, regulated industries, or long-term engagement may take several weeks.
The process usually involves business owners, procurement, legal, finance, IT, security, compliance, and the internal team that will work with the vendor. For software development projects, technical leadership should be involved early.
An outsourcing vendor should provide company registration documents, security policies, compliance evidence, case studies, client references, financial indicators, insurance information, delivery process documents, contract templates, SLA terms, and IP ownership terms.
You can assess vendor security by reviewing certifications, access control policies, incident response processes, data protection practices, penetration test reports, vulnerability scan results, secure development practices, and employee security awareness.
No. Due diligence should continue throughout the outsourcing relationship. Vendor performance, security posture, compliance requirements, and delivery risks can change over time. Regular reviews help keep the partnership healthy and reduce long-term risk.
Let’s start with Sunbytes
Let us know your requirements for the team and we will contact you right away.


